At the start of March, I had the opportunity to join the Araintel team to cover RootedCon 2026, one of the leading cybersecurity events. This edition brought together more than 270 experts and attracted more than 10,000 attendees. Over these days, we learned about cybersecurity, discussed human rights, and dreamed about the future.
Below, I share my experience with you, highlighting the points that caught my attention most, along with a summary of the talks I managed to attend. You can also read my raw notes via this Mastodon thread.

Impressions of a first-timer
I must admit that RootedCon intimidated me. I was expecting, from the experiences of acquaintances and press coverage, an extremely high-level event. Would I be up to it? I wondered.
An accessible niche
I had braced myself for this high level of the sessions, but I was pleasantly surprised by how accessible this event is for all audiences.
The first contact could not have been better, as the organisation was friendly and always had a smile on its face. There were talks for all levels, and in the more technical sessions, the speakers made sure to cover the basics. Finally, there were activities that even children could enjoy, such as the soldering workshop, the robot battle, and the exhibition of cryptographic machines.

The whole ecosystem
RootedCON brings together cybersecurity researchers, service providers, communities, activists, and all kinds of people across the cybersecurity ecosystem. It is quite an achievement to create a space where such diverse profiles can collaborate.
Too much going on
RootedCon featured eight tracks on the first day, seven on the second, and four on the third. That is an incredible number of interesting talks. There was always an engaging session to attend, an activity to participate in, or someone to chat with in the corridors. I gave it all at first, afraid of missing anything interesting, and perhaps I pushed myself too hard. Next time I’ll take it easy.
This is also why this chronicle only covers a small part of what the event had to offer. Do check the hashtag #RootedCon on your social media to find out everything that happened.
Hot topics
Although a wide variety of subjects were discussed during the event, certain ideas resonated and kept repeating.
La Liga’s blocks: There is considerable concern about the fact that whenever there is a football match in Spain, half the internet is blocked, including access to essential services.
The shadow of Chat Control: The threat of Chat Control, the European Council legislative proposal seeking to spy on all our communications, has not entirely disappeared. Similar proposals continue to be debated under the pretext of protecting “the children”, and we must stay vigilant. Along similar lines, the push for age verification is a source of great concern for security experts due to its privacy and freedom-of-speech implications.
The role of AI: Artificial intelligence is everywhere, and was the subject of many conversations. What is our role in a world where machines do our work? What new cybersecurity and privacy risks is AI creating? How can we make appropriate use of artificial intelligence? These are questions for which we are still finding the answers.
Collaboration is key: In the fight against cyberattacks, public bodies are united and work together. It is the only way to win this battle.
Session roundup
The quality of the presentations was supreme. Every session I attended was packed with fascinating information delivered in a highly engaging manner. Here is what caught my attention.
Keynote
by Arantxa Sanz Gil and Román Ramírez

The opening of events is not usually anything special. Figures are reviewed, ground rules laid out, and that is about it.
Here, however, things kicked off with a bang, with a mention of the legal proceedings RootedCon is pursuing against “La Liga” over the internet blocking issue. We were told that the matter is awaiting a ruling from the constitutional court, plus they are closely monitoring how the situation is unfolding with the blocking of VPNs.
Inside the machine: The war on Digital Rights in Europe

Patrick Breyer, a member of the German Pirate Party, told us how close we came to losing our rights with Chat Control and gave us an overview of how European politics works and what citizens can do to fight for their rights effectively.
- There are shadowy powers and lobbies that wield enormous influence over regulations.
- Social pressure is a very effective weapon.
- Tools such as fightchatcontrol.eu are extremely useful. Educating people about the dangers of certain regulations and providing them with tools is powerful.
Inside the Apple Orchard: 20 years of macOS Malware TTPs
by Daniel Lastanao Miró and Ricardo J. Rodríguez
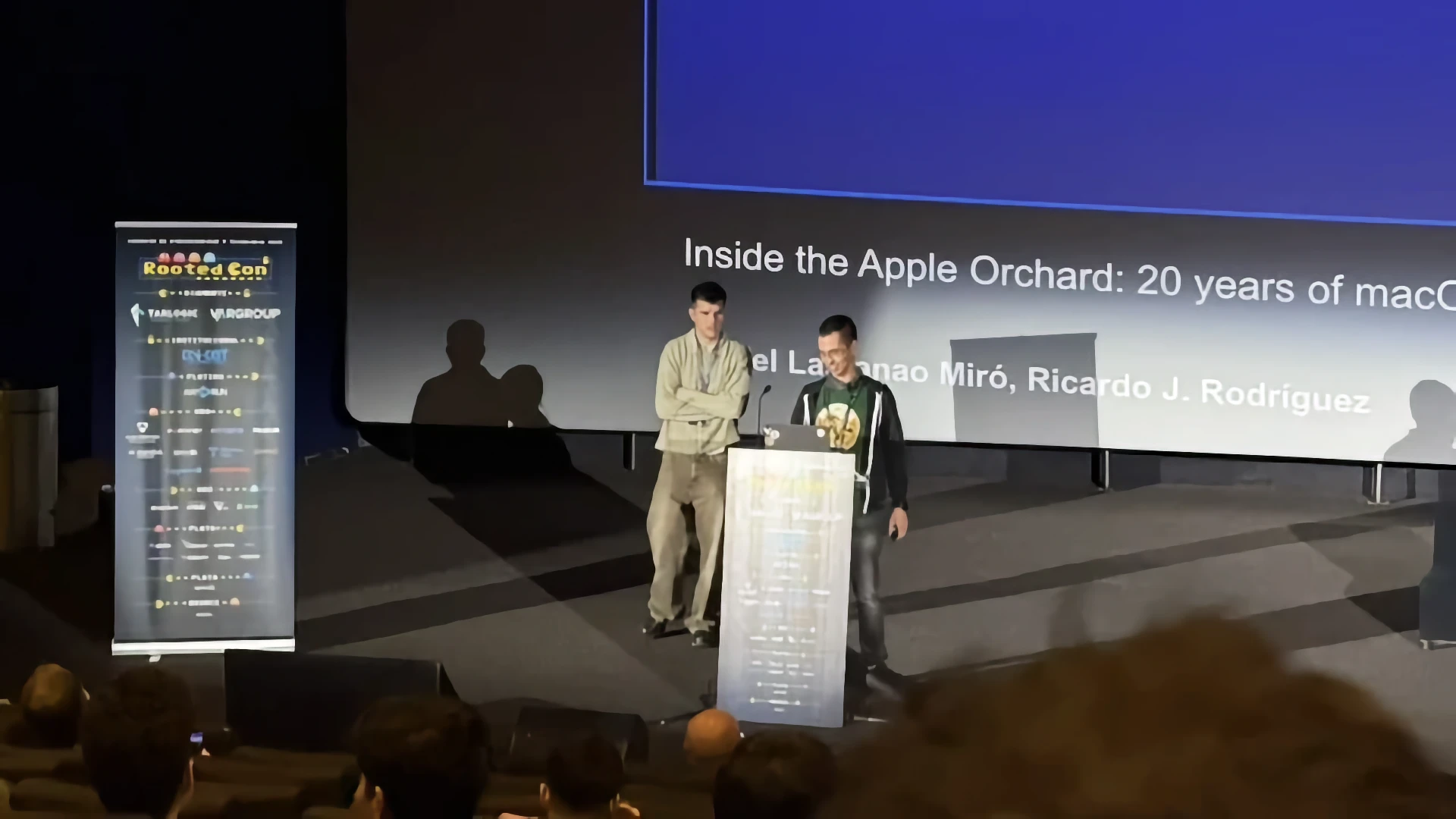
Daniel and Ricardo, from the RME-DISCO research group at the University of Zaragoza, debunked the myth that Macs are free of malware.
- Malware exists on macOS, and in considerable quantities.
- It consists predominantly of adware and information theft.
- It adapts rapidly to new times, bypassing new security controls and adjusting to architectural changes.
Do not miss the Araintel article covering this talk in greater detail.

Elche: The intimate diary of a cyberattack
by Josué Castillo and Mª Asunción Brotóns

Josué and Mª Asunción recounted how they experienced the cyberattack on the town council’s infrastructure, and how the recovery has been progressing. They emphasised the need for:
- Cooperation between administrations.
- Action plans prepared in advance.
- Sharing the experience publicly.
Does your AI agent know too much? A practical look at Confidential Computing
by Pablo González and Laura Lacarra Arcos

Laura and Pablo addressed the security risks associated with AI agents, which access all our personal information to automate everyday tasks such as replying to emails or managing connected devices.
In their talk, Laura and Pablo demonstrated how easy it is for an attacker to read the data “in use”. They explained the concept of Confidential Computing and how programs can use attestations to ensure that the data they use is encrypted in memory.
Do not miss my interview with Laura Lacarra for Araintel, in which she discusses these topics in detail.

Novel Linux persistence techniques. MITRE ATT&CK and the tunnel effect
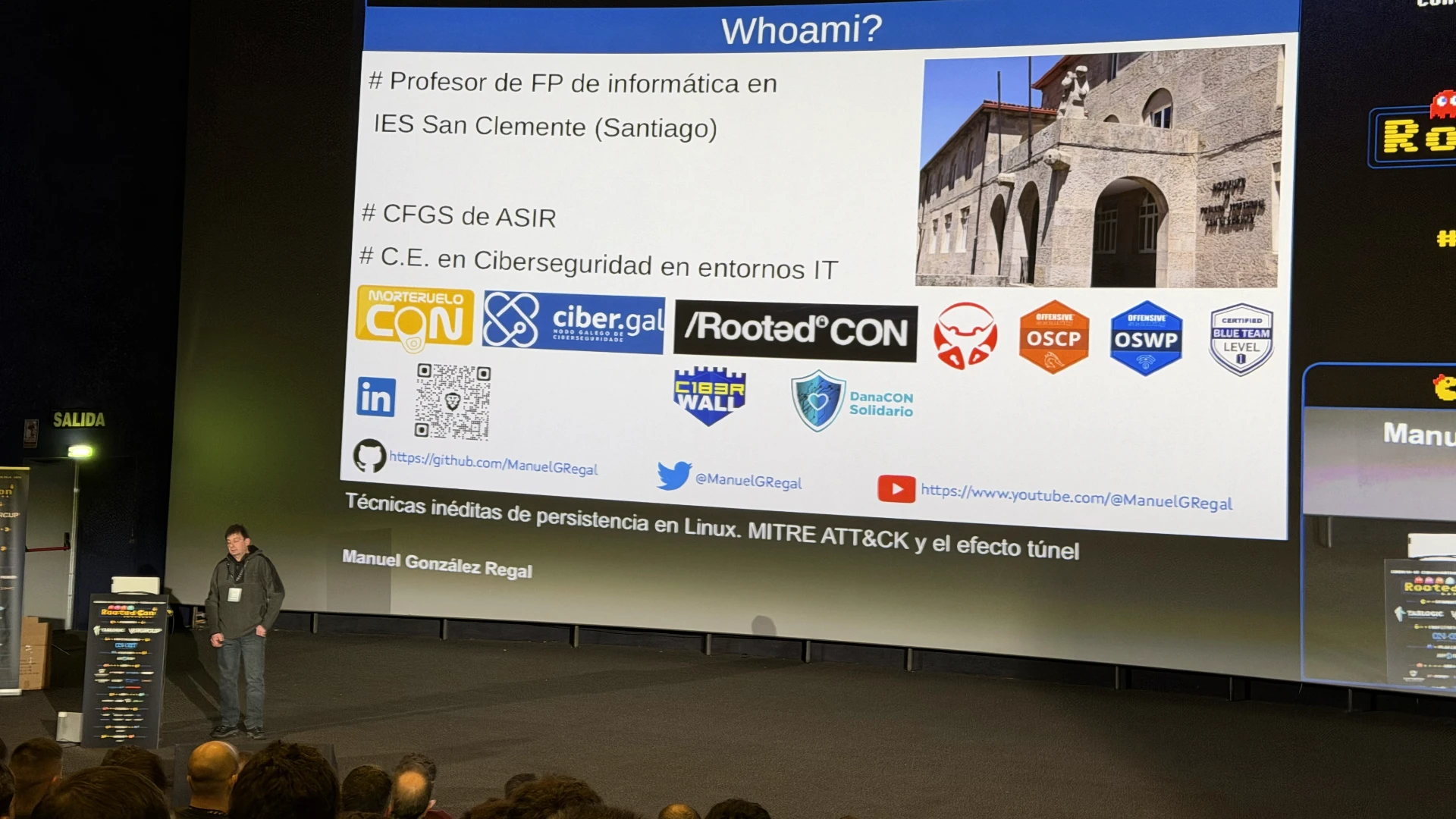
Manuel gave us a masterclass on how attackers leave backdoors open to maintain a foothold in the systems they compromise.
He went into detail on how configuration options, originally created to improve security, can be abused. He highlighted little-known OpenSSH configuration options, specifically those that define commands to be executed when certain events occur.
Find out more about this topic in the extended session summary I wrote for Araintel.

The place of people’s rights in the cyber sphere
Round table with Ofelia Tejerina, Simona Levi, Borja Adsuara, Cristóbal Gázquez and Jorge Dávila
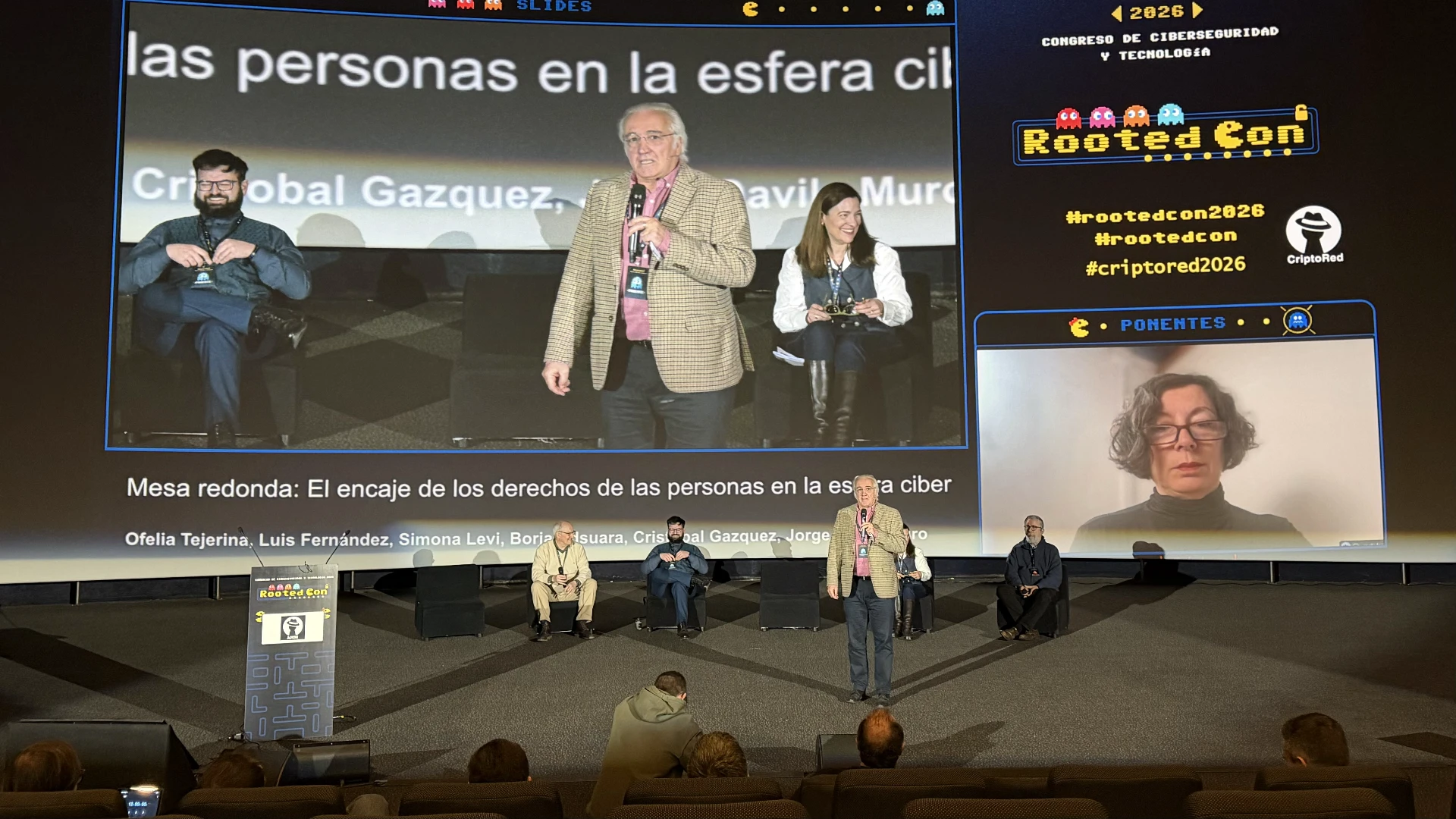
Finally, in this round table, several prominent figures from the legal world warned us about:
- The danger of censorship “against things we dislike”, since blocking content that is not illegal sets very dangerous precedents.
- The importance of anonymity as a tool for freedom of speech.
- How “the children” are being used as an excuse to gain control of communications. We already have mechanisms in place to guarantee the safety of minors, and in most situations, parents are simply abandoning their responsibilities.
Some quotes that stuck with me:
- “The easy solution is to turn the internet into a soft play centre. They would never think of putting an ID check at every town square, but they have no qualms about doing it online.”
- “Disinformation is a business, but freedom of speech is not.”
- “Parents say they don’t understand mobile phones, but when they want to have an affair, they learn how to hide their conversations.”
- “Shall we block access to the sea so that children don’t drown?”

Connect With Your Audience
We are experts at crafting stories that connect with your clients’ pains and position your product strengths organically.
Book a Call